RsaCtfTool
RSA attack tool (mainly for ctf) - retrieve private key from weak public key and
Python5273gpl-3.0
6 days ago
cryptographyrsarsa-attack
ssh-auditor
The best way to scan for weak ssh passwords on your network
Go590other
5 months ago
auditingbrute-forcediscover
weakable-self
A Swift micro-framework to easily deal with weak references to self inside closu
Swift78mit
3 years ago
closuresiosmemory-management
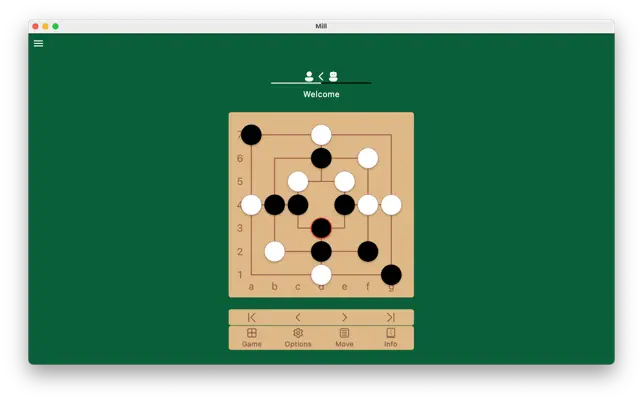
Sanmill
Description Mill Game program, which supports rule variants.Rules:* A player
Dart131gpl-3.0
19 hours ago
aialpha-beta-pruningbitboard
SEC
Seed, Expand, Constrain: Three Principles for Weakly-Supervised Image Segmentati
Jupyter Notebook240mit
6 years ago
SEC
Seed, Expand, Constrain: Three Principles for Weakly-Supervised Image Segmentati
Jupyter Notebook241mit
6 years ago
poke-types
🔥💧🍃 Pokémon types, including — their weaknesses, strengths and immunities.
JavaScript8mit
last year
gamegame-freakmodule
phpcs-security-audit
phpcs-security-audit is a set of PHP_CodeSniffer rules that finds vulnerabilitie
PHP701gpl-3.0
last year
phpphp-codesnifferphpcs
RsaCtfTool
RSA attack tool (mainly for ctf) - retrieve private key from weak public key and
Python5273gpl-3.0
6 days ago
cryptographyrsarsa-attack
ssh-auditor
The best way to scan for weak ssh passwords on your network
Go590other
5 months ago
auditingbrute-forcediscover
snorkel
A system for quickly generating training data with weak supervision
Python5605apache-2.0
6 months ago
aidata-augmentationdata-science
weakable-self
A Swift micro-framework to easily deal with weak references to self inside closu
Swift78mit
3 years ago
closuresiosmemory-management
Sanmill
Description Mill Game program, which supports rule variants.Rules:* A player
Dart131gpl-3.0
19 hours ago
aialpha-beta-pruningbitboard
SEC
Seed, Expand, Constrain: Three Principles for Weakly-Supervised Image Segmentati
Jupyter Notebook240mit
6 years ago
SEC
Seed, Expand, Constrain: Three Principles for Weakly-Supervised Image Segmentati
Jupyter Notebook241mit
6 years ago
poke-types
🔥💧🍃 Pokémon types, including — their weaknesses, strengths and immunities.
JavaScript8mit
last year
gamegame-freakmodule
phpcs-security-audit
phpcs-security-audit is a set of PHP_CodeSniffer rules that finds vulnerabilitie
PHP701gpl-3.0
last year
phpphp-codesnifferphpcs